【System】White Paper on Network Security Technology of Charge Pile
Notice Number:White Paper on Network Security Technology of Charge PileAuthor:StarChargePublication Date:2023/08/15
1. Scope of Application
This document is applicable to all series of DC, AC and integrated, energy storage products in the field of charging stakes.
2. Normalized Introduction File
This chapter mainly refers to the SDL security development process, ISO 62443 series of documents.
3. Common Terms&Definition
Secret Key Management: Manage the life cycle of keys such as key generation, distribution, storage, update, archiving, revocation, and destruction.
CVE: Common Vulnerabilitis & Exposures
SSH: Secure Shell Protocol
SYN: Synchronousidle
SFTP: Security File Transfer Protocol
XSS: Cross Site Scripting
HTTPS: HyperText Transfer Protocol Secure
ARP: Address Resolution Protocol
DNS: Domain Name System
4. Safety Frame of Charging Pile
This chapter establishes and standardizes a functional framework for mitigating common security threats to charging pile(see Chapter 7 for details). See Figure 1 for details.
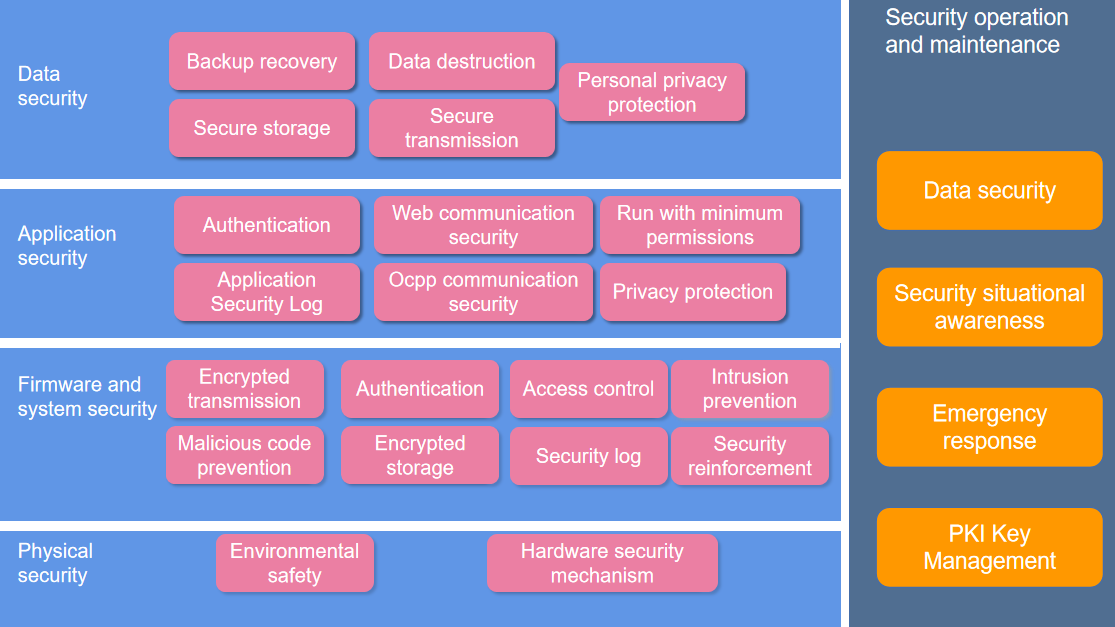
Figure 1 Security framework of charging pile
The security framework of charging pile is divided into five levels: physical security, firmware and system security, application security, data security, operation and maintenance security. The main security functions of each level are as follows:
1) physical security
At the physical layer, the charging pile needs to correspond to the surrounding environment security and hardware security mechanisms.
2) firmware and system security
Charging pile has backup recovery, secure storage, personal privacy protection, secure transmission, data destruction at the operating system level.
3) application security
The charging pile has authentication, web communication security, ocpp communication security, minimum privilege operation and application security log in the application layer.
4) data security
Charging pile has backup recovery, personal privacy protection, secure storage, secure transmission and data destruction in data security level.
5) operation and maintenance security
In the aspect of security operation and maintenance after the charging pile is listed, it needs PKI key management, emergency response, security situational awareness, and security auditing.
5. Development Process of SDL for Charging Pile
Charging pile products follow Security Development Process Specification, and follow the SDL development process from product development to emergency response and vulnerability management.
a. product development security process
The product development process follows the process of product threat model, security requirements development, security coding, security testing, open source and tripartite library management.
b. vulnerability management
During the effective life cycle of a product, if a security vulnerability occurs, the affected product model and version can be safely audited, and vulnerability repairs can be made in a timely manner.
c. security emergency response
When a product is disrupted by an earthquake, fire, natural disaster, or an external network attack, an emergency center can quickly troubleshoot problems and ensure business recovery.
6. Security Function Requirements for Charging Pile
6.1 Physical Layer Security
This level mainly includes the following contents
1.The equipment shall meet the safety requirements under the conditions of low temperature, high temperature and constant damp heat.
2.The equipment shall meet the immunity requirements of radio frequency electromagnetic field radiation immunity.
3.Only physical ports (JTAG port、SD card、RS232/485、RJ45network port) are provided to prevent unauthorized interfaces from accessing the internal resources of the charging pile system.
4.Enable the hardware security mechanism for the charging pile equipment. The best practices include the following:
(1) Use non universal screw types, or use materials such as ultrasonic welding or high temperature glue to seal multiple hardware enclosures together.
(2) Remove the chip mark, use epoxy resin to hide the mark, or use metal shell to encapsulate the chip to protect sensitive chips and components.
6.2 Firmware and Operating System Security
This layer mainly includes the following contents
6.2.1 Network Communication Security
This security function can prevent SYN flooding and malformed messages, ARP spoofing, DNS spoofing and other common network communication attacks.
6.2.2 Authentication
This security function mainly corresponds to the following requirements
(1) The user who logs in to the charging pile shall be identified and authenticated, and the identification shall be unique.
(2) No login mechanisms such as special instructions, password free accounts, and special combination keys that do not require authentication are allowed to ensure that the authentication mechanism will not be bypassed.
(3) If the authentication authentication uses the account password to log in, the setting of the corresponding key must meet the security requirements of the account password. (See 6.5.1 Column 2)
(4) It has an anti brute force cracking mechanism to increase the limit on the number of consecutive login failures of the device.
(5) There is a login timeout exit mechanism, which needs to be reset after a certain time.
(6) In the process of remote login, measures should be taken to verify whether the information is tampered and eavesdropped during network transmission.
6.2.3 Permission
The main requirements for this security function are as follows:
(1) Implement the principle of minimum authority operation for the charging pile, and distinguish between ordinary users and administrators.
(2) Only authenticated users are allowed to perform operations within the scope of authorization.
6.2.4 Logging and Auditing
The main requirements for this security function are as follows:
(1) It supports the logging function, which should cover all users, and supports the audit of important user behaviors and important security events.
(2) It supports recording important security events such as startup, shutdown, restart, upgrade, configuration modification, and full storage space of the charging pile system.
(3) The log format needs to include information such as time, source, event type, and whether the event was successful, so as to facilitate subsequent security log audits.
(4) Security logs need to be protected to prevent unauthorized or unexpected deletion, modification, and overwriting.
(5) Support the upload of audit logs to the log server platform to ensure that the retention time of security audit logs is not less than 6 months.
(6) Ensure that the log, debugging information and alarm information of the charging pile do not contain any account password, personal identity information, name, telephone and other sensitive information that has not been encrypted or desensitized.
6.3 Application Security
6.3.1 Web Communication Security
This requirement is mainly aimed at the following functions of the charging pile on the premise of supporting the web server function
(1) By default, SFTP, HTTPS, SSH and other security protocols are enabled for upload, download, request and response. To ensure the security of web communication, if users actively open the non security protocol, they need to give a risk prompt.
(2) The validity of the requested data needs to be verified, and the data that has not passed the verification needs to be rejected to prevent SQL/command injection and XSS attacks.
(3) Support session timeout exit mechanism.
(4) In the process of Web communication, when it is detected that the user's IP address and other information have changed, it is necessary to forcibly exit the session and perform authentication again.
(5) When you log in to the Web, you need to record and display the IP address information of the login party.
6.3.2 Authentication
The main requirements for this security function are as follows:
(1) The user who logs in to the charging pile shall be identified and authenticated, and the identification shall be unique.
(2) No login mechanisms such as special instructions, password free accounts, and special combination keys that do not require authentication are allowed to ensure that the authentication mechanism will not be bypassed.
(3) If the authentication authentication uses the account password to log in, the setting of the corresponding key must meet the security requirements of the account password. (See 6.5.1 Column 2)
(4) It has an anti brute force cracking mechanism to increase the limit on the number of consecutive login failures of the device.
(5) There is a login timeout exit mechanism, which needs to be reset after a certain time.
(6) In the process of remote login, measures should be taken to verify whether the information is tampered and eavesdropped during network transmission.
6.3.3 Permission
The main requirements for this security function are as follows:
(1) Implement the principle of minimum authority operation for the charging pile, and distinguish between ordinary users and administrators.
(2) Only authenticated users are allowed to perform operations within the scope of authorization.
6.3.4 Logging and Auditing
The main requirements for this security function are as follows:
(1) It supports the logging function, which should cover all users, and supports the audit of important user behaviors and important security events.
(2) It supports recording important security events such as startup, shutdown, restart, upgrade, configuration modification, and full storage space of the charging pile system.
(3) The log format needs to include information such as time, source, event type, and whether the event was successful, so as to facilitate subsequent security log audits.
(4) Security logs need to be protected to prevent unauthorized or unexpected deletion, modification, and overwriting.
(5) Support the upload of audit logs to the log server platform to ensure that the retention time of security audit logs is not less than 6 months.
(6) Ensure that the log, debugging information and alarm information of the charging pile do not contain any account password, personal identity information, name, telephone and other sensitive information that has not been encrypted or desensitized.
6.4 Data Security
6.4.1 Data Transmission Security
This requirement mainly includes
(1) Password technology is used to ensure the integrity of data transmission.
(2) Password technology is used to ensure the confidentiality of data transmission.
6.4.2 Data Backup and Recovery
This item requires that the corresponding data have channels to restore the default factory configuration (factory configuration file, key file, boot file), which can be used to restore factory settings.
6.4.3 Data Destruction Security
This item is mainly about the channel for the thorough destruction of data. (SSD cannot be processed by degaussing and formatting)
6.5 Operation and Maintenance Security
This security function mainly needs to meet the following functions.
6.5.1 Account Security
(1) Delete or deactivate redundant and expired accounts in a timely manner.
(2) The complexity of user passwords shall at least include numbers, uppercase and lowercase letters, and special characters, and the length shall not be less than the strength of 8-digit passwords, or risk prompts shall be given to users.
(3) All user names and passwords need to support user modification, and hard coded passwords are not allowed.
(4) When the user logs in to the system for the first time, he/she shall be forced to modify the default password of the user
(5) Account separation shall be ensured. The account used for inter program communication and the account for system maintenance shall be separated.
6.5.2 Secret Key Management
By default, it is required to prohibit the known insecure key algorithms in the industry from key negotiation, digital signature, sensitive data encryption and other scenarios. The following insecure algorithms cannot operate in the above scenarios.
Table 1 List of unsafe algorithms
Algorithm | Algorithm Type | Application scenario |
MD2/MD4/MD5 | hash function | digital signature |
SHA-0/SHA-1 | hash function | digital signature |
DES/3DES | symmetric encryption | symmetric key encryption |
RC4 | symmetric encryption | Wifi WEP mode |
RSA/DSA(1024) | asymmetric encryption | firmware digital signature |
ECDSA(160bit) | elliptic curve | firmware digital signature |
6.5.3 Vulnerability Management
It is necessary to provide users with vulnerability feedback channels, vulnerability repair mechanisms, and risk reduction schemes during vulnerability repair.
6.5.4 Emergency Response
The company needs to have an emergency response center to deal with the backup plan of security problem vulnerability repair and business impact in a timely manner.
7. Common Security Threats of Charging Pile
Table 2 Common Threats of Charge Point and Countermeasures
Threat source | Threat technology | Countermeasures |
Physical layer
| Device turned on | The system identifies exceptions and generates alarm information |
Device moved | The system identifies exceptions and generates alarm information | |
Physical interface is connected privately | Minimize physical interfaces | |
Physical insertion and removal of SD card | Local data encryption | |
Private plugging and network connection | Access authentication | |
Firmware and operating system layer | Network attacks such as flooding and malformed packets | Configuration of network access control policies such as flow control and white list |
Vulnerability exploitation | Minimized system installation, factory vulnerability repair, default enabling of security communication protocol, protocol reinforcement configuration, and Web communication security | |
Port scanning | Port minimization on | |
Firmware tampering and machine brushing | Safe boot | |
System intrusion | Intrusion detection | |
Malicious code implantation | Malicious code detection | |
Application layer | Identity counterfeiting | Identity authentication (login password, certificate verification) |
Command injection | Request parameter detection | |
XSS attack | Request parameter detection | |
Session hijacking | Web login verification code, login timeout | |
Malicious software | Digital signature and verification of software package | |
Access violation | Identity authentication, access control, sandbox isolation mechanism | |
Ultra vires execution | Minimize Authorization | |
Data layer | Data tampering | Integrity check |
Data leakage | Security communication protocol, data encryption and key management mechanism, log audit | |
Privacy Data | Auditing personal privacy data | |
Operation and maintenance layer | Brute force password | Set mechanisms such as password complexity detection, forced modification of the manufacturer's default password for the first login, password expiration detection, and regular modification |
Operational repudiation | Logging and auditing | |
Unsafe algorithm cracking | The known insecure protocols and cryptographic algorithms are disabled by default | |
Key cracking/disclosure | Secret key management |
